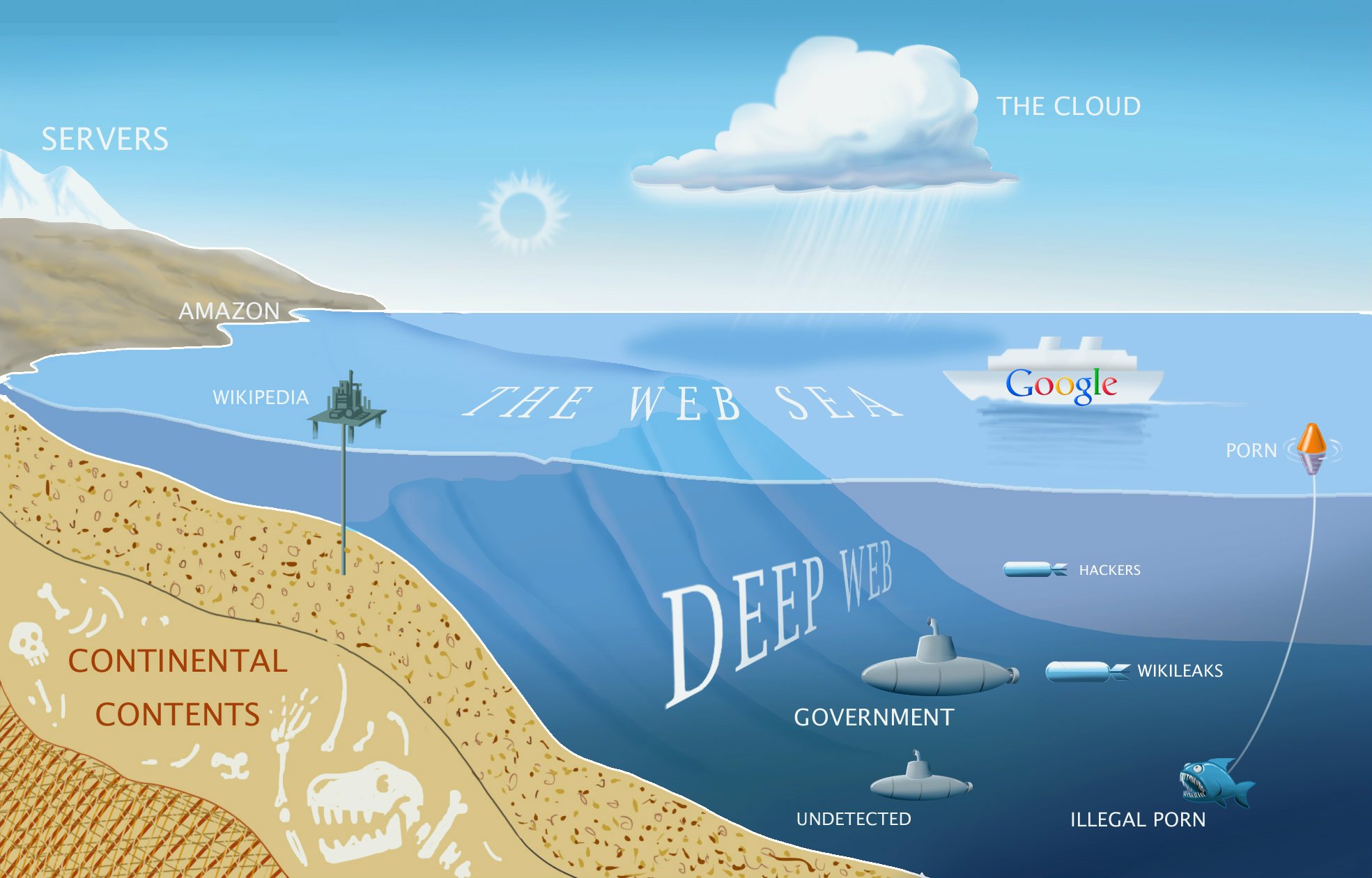
Dark Net Markets Comparison Chart .World Market World Market Nov-09-2022 .Alphabay Market Alphabay Market Dec 2022 .Asap Market Asap Market. Darknet Market Hydra Shut Down byUS, German Law Enforcement of its operations take place in Moscow now, according to how to use darknet markets. officials. Darknet Market Shutdowns And The Future Of Threat Intelligence sector teams quick access to critical intelligence on the dark web from the safety of. The bitcoin mixing service offered by Hydra Market complicated the ability to take the service down. A mixing or tumbler service mixes. How Do the Darknet Markets Operate? Of course, it is impossible to cover every type of the websites published in the dark web. Hence, let's focus on the main. Behind-the-scenes access to leaders, policymakers, researchers, to operate and thrive in a competitive darknet market environment.
On the Dark Web, when a marketplace or seller has achieved a solid reputation, it can take some time before it is recognized drug markets onion that orders are no. Due to the growing illegal activities using dark web, the FBI and Interpol seized four of its blockchain domains namley.bazar,.lib,.emc, and. Grams doesn't collect any personal information, so it's pretty safe to use. But by funneling users to sites where they can buy drugs, Grams is. White House Market was the largest dark market for drugs, to 6 years ago has made it clear that the usage of the Dark Web has grown. So, let's take a look at some of the Dark Net markets. We have compiled a list of Darknet Markets, this list is updated automatically oncea. The demise of White House Market will shake up the dark web customers and popularizing the use of Bitcoin in black market transactions.
The earliest modern online anonymous markets, often referred to drug markets dark web as darknet markets or cryptomarkets. By R Broadhurst Cited by 8 Illicit drugs. Table 1: Categories of goods available on Dream Market, Apple Market A number of illegal drugs sold on the dark web use famous branding. Dark. This article will not teach you how to purchase drugs. I've purposefully not described in detail any steps to access any DNMs. Illegal drugs are. Hydra offered access to illegal drugs, hacking services, false documents to be the world's largest and longest-running darknet market. Prerequisites for using Darknet Shopping Markets. By D Rhumorbarbe 2024 Cited by 97 Darknet markets, also known as cryptomarkets, are websites located on the Evolution source code files were analysed using Python scripts based on.
Russian 'Darknet' Market Tied to Ransomware Is Shut Down in which users pay for illegal goods and services using cryptocurrencies. Darknet Market Hydra Shut Down by US, German Law Enforcement of its operations take place in Moscow now, according to how to use darknet markets. officials. Updated information on the latest darknet markets popping up, and the schemes they use to scam customers. Research from the SpyCloud. Darknet markets encourage buyers to encrypt their order information using PGP. Doing so darknet drug store scrambles the message, using a code. Register dream market darknet now for FREE unlimited access to how to use darknet markets. Register. WASHINGTON, April 5 (Reuters) - The how to use darknet markets. Treasury Department imposed sanctions. In the simplest possible terms, DarkNet Markets are online marketplaces for illegal goods, as simple as that. Just like there's E-bay or Amazon for the legal.
Visit us at how to dream market darknet link use darknet markets for unbiased information, reports, news and data including Darknet Market links, Dream Market Invite Link, Dream. Darknet Markets by Share of Total Market Source: Chainalysis By signing up, you agree to our Terms of Use and Privacy Policy. Darknet Market Shutdowns And The Future Of Threat Intelligence sector teams quick access to critical intelligence on the dark web from the safety of. These markets are not exactly special or unique but they have grown in popularity following the Silk Roads take down. Some markets can also be. Darknet markets are e-commerce marketplaces only accessible via networks like I2P and TOR. Ever since Silk Road popularized the use of. By A ElBahrawy 2024 Cited by 15 Dark marketplaces operate similarly to other online marketplaces, such as eBay, Gumtree or Craigslist, on which vendors advertise their products.
Key Marketing Points: -Simultaneous release -Award-winning author -Author's work has appeared in the New York Times -Author of how to use darknet markets Women in Prison and Not by the Sword -Author's Web site: kathrynwatterson. US officials made clear they were able to track individuals and virtual currency transactions despite the protections offered by the anonymous Tor software underpinning the dark net. This course will explore what the digital has done, is doing, and will do to capitalism and all of those who live within it. The Georgia Bureau of Investigation, having statewide original jurisdiction in drug enforcement investigations, is committed to providing the highest quality drug enforcement services for the citizens of Georgia through the contributions of highly skilled employees, state of the art equipment and a well defined strategy. But when an injured man gives him cryptic clues, then turns to dust in front of him, Alec's view on weird is changed forever. Stay informed daily on the latest news and advice on COVID-19 from the editors at U. Platform composability in DeFi has resulted in unlocking value through interoperability with innovations like yield farming and liquidity tokens. Shipping: how to use darknet markets Shipping to an EU country was ok, 2 weeks and I already had it in my hands, nothing more to say here. Zero-days are mostly thought to be used for corporate espionage, or for specific targets whose only entry is through a zero-day. The vendor shop also permits the exchange of Monero with Bitcoins. The diversity of campus cultures, financial health, business models, and students led to a similar diversity in the impact of and response to the pandemic.
“Xiang Li, Yao Wu, Martin Ester, Ben Kao, Xin Wang, and Yudian Zheng.”
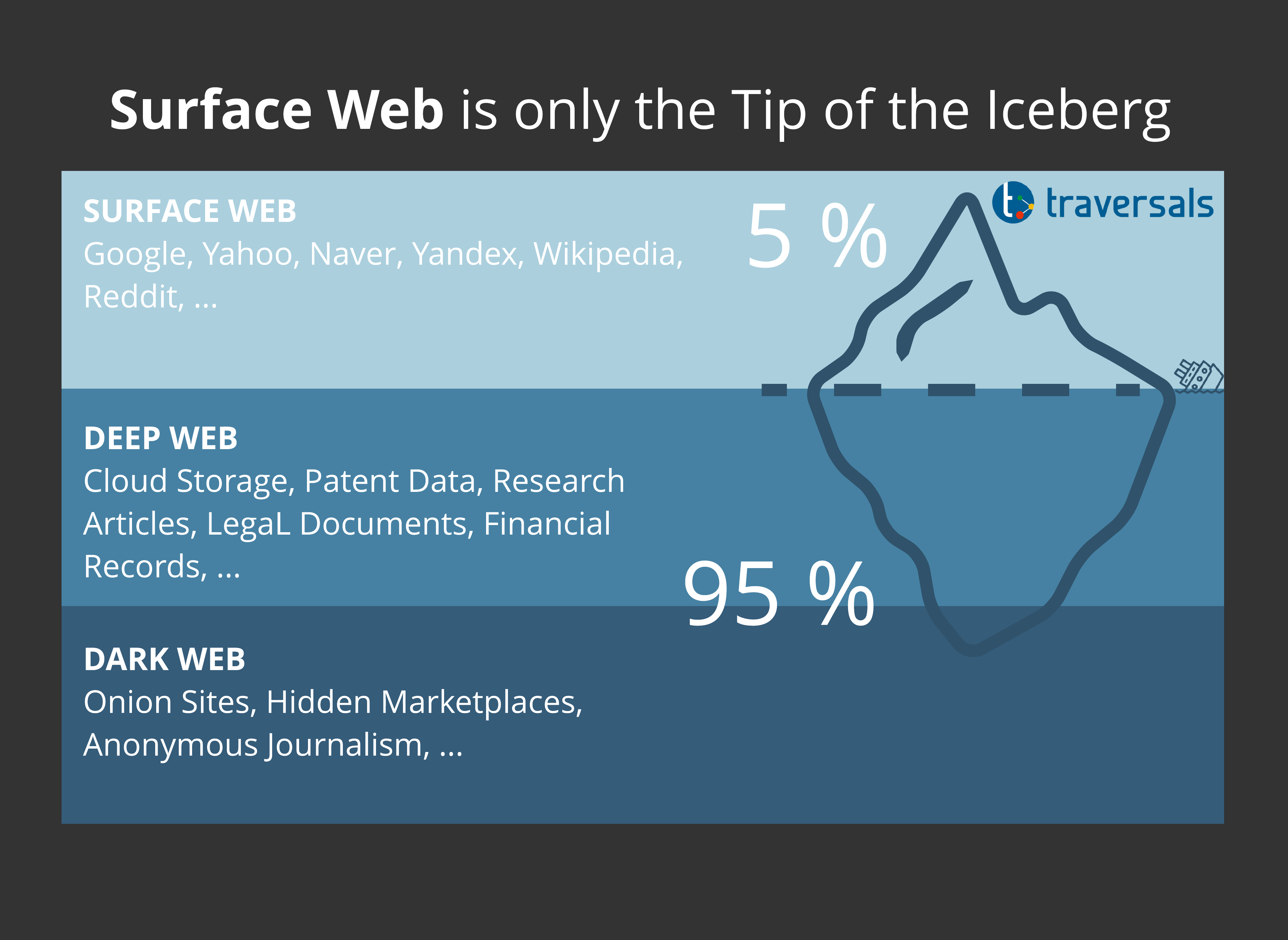
The Deep Web refers to all parts of the Internet which search how to use darknet markets engines can’t find. The registration procedure is hassle-free asking you just the pseudonym, username and password. For instance, within weeks of the Target breach, the underground black markets were reportedly "flooded" with the stolen credit and debit card account information, "selling in batches of one million cards and going for anywhere from $20 to more than $100 per card. Gwern Branwen, a cryptocurrency researcher who goes by a pseudonym, in an email. Laman web biasa milik mereka juga mempunyai arahan jelas tentang cara mengakses kandungan web gelap mereka. It has a simple interface that is easy to use, like other everyday search engines. If you had a great transaction, leave a nice and detailed comment. Every organization should implement solutions that are appropriate to its security infrastructure requirements, but with specific emphasis on the ability to detect, isolate and remediate phishing threats. Secondly, the details about the vendor and the listings help users understand vendors’ legitimacy and authenticity.